Late this morning, countless AIM accounts dropped offline. For reasons known only to Aol, the company decided today was a good day to reset a limited range of user passwords without warning. It was abrupt, but companies do this every time there's a data breach, or sometimes just to make sure people are using strong passwords.
Normally this is no big deal — you just go through the reset routine. But Aol is not a normal company, and AIM is not a normal service. AIM is too old for this kind of stuff:
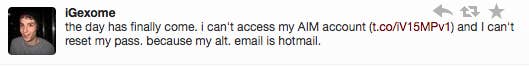
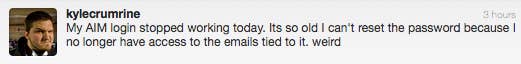
The email account I used to register my first AIM address hasn't been active for years, so I couldn't use it to get through the password reset routine. Thankfully, my security question is about where I was born — a stupid security question, by the way — so that worked fine. My coworker's was about her pet's name, which she filled out when her dog was still alive (RIP). Again: AIM is old.
Aol recently laid off most of the non-support employees in the AIM group and put the service out to pasture. But this alone doesn't seem like enough of a reason to just up and reset everyone's passwords. Was something wrong? Was there an exploit we didn't know about? Or is a disgruntled AIM team just fucking around with us?
