Yesterday, an as-of-yet still unknown "hacker" released the private information of more than a dozen celebrities, leaking their phone numbers, mortgages, and Social Security numbers online.

To call this a hack, though, isn't quite right. It's actually a fairly straightforward process.
The first step is to head to a city or town's mortgage registry.
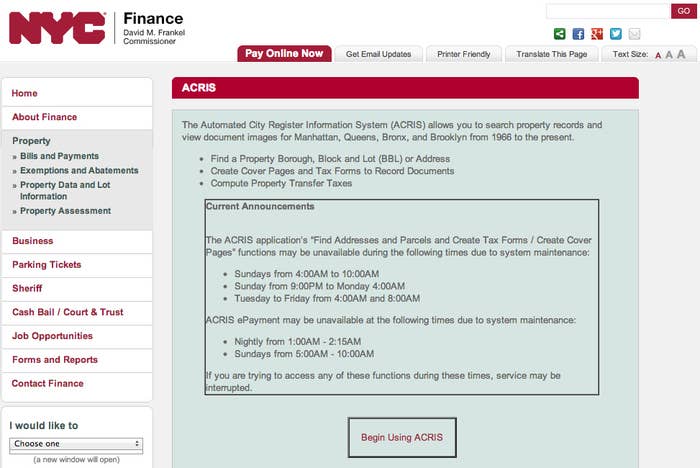
New York City's system, known as ACRIS, prompts you for a name and a set of dates to search for documents within. Nothing more than what you could find on Wikipedia.
Here's the ACRIS directory of properties associated with the name Michael R. Bloomberg, registered after January 1, 2002 (when he was elected mayor).
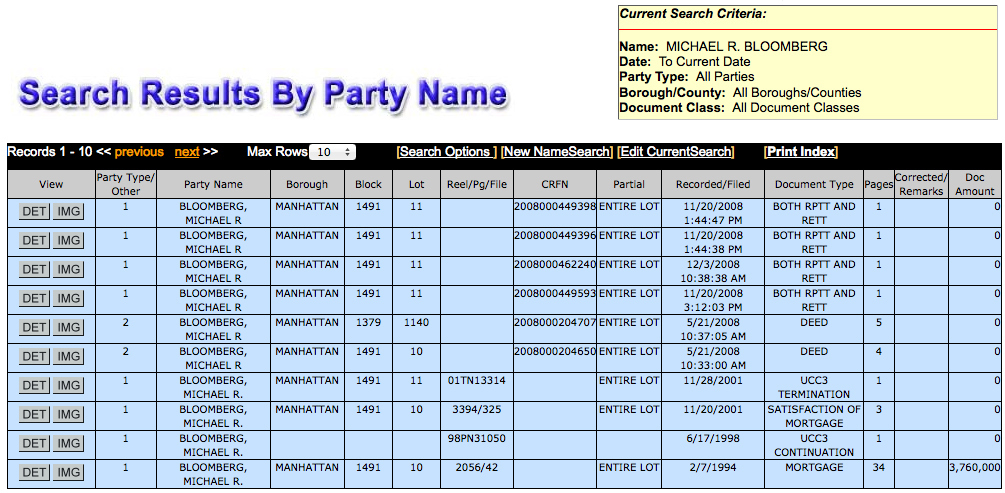
With enough searching through these kinds of documents you can grab almost everything you need for a "credit hack."

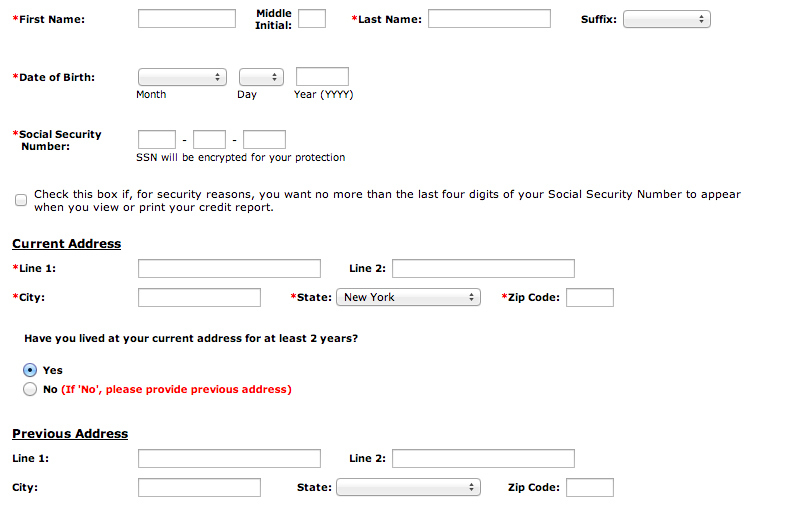
Annualcreditreport.com is a site that's been involved with a few of these "credit hacks."
The site requires only cursory biographical information and a social security number. An early mortgage might include a Social Security number, and you already have a list of previous addresses.
Equifax, a data security company associated with Annualcreditreport.com, released a statement Tuesday confirming that someone did breach their records:
"At Equifax, data security is paramount and we have stringent security measures in place for protecting the data entrusted to us.
Equifax enables consumers to access their credit reports through a variety of channels, including annualcreditreport.com which is a free service. In order for a consumer to have access to their credit report through this channel, they must provide Personally Identifiable Information (PII) that should be known only to the individual.
We are aware of recent media reports pertaining to unauthorized access to files belonging to high-profile individuals. Equifax can confirm that fraudulent and unauthorized access to four (4) consumer credit reports has occurred through the annualcreditreport.com channel, a free public service that allows all consumers to get annual access to their credit report. Our initial investigation shows the perpetrators had the PII of the individuals whose files were accessed and were therefore able to pass the required authentication measures in place. We have launched a full investigation into this matter and we are also working closely with law enforcement authorities on this matter."
This is not an obscure procedure, either:
A political campaign researcher, who wished to remain anonymous, told BuzzFeed this type of research is very basic. "I do this on every client I have — and their opponent," he said. "This was not some super-secret hack. This was just basic research."
Nor is this is a new problem in the data security world:
Wired covered a paper written by Christopher Soghoian, a fellow at Harvard's Berkman Center, in 2009, in which he outlined a myriad of ways "credit hackers" could very legally mine out someone's personal financial history.
From his paper's abstract:
"This paper will present a number of loopholes and exploits against the system of consumer credit in the United States that can enable a careful attacker to hugely leverage her (or someone else's) credit report for hundreds of thousands of dollars. While the techniques outlined in this paper have been used for the personal (and legal) profit by a small community of credit hackers, these same techniques could equally be used by more nefarious persons — that is, criminals willing to break the law, engage in fraud, and make off with significant sums of money."
In April of 2012, Time Business wrote about this very simple form of data mining:
Time provided a step-by-step process of how to expose someone's financial history legally. Geoff Webb, director of product marketing at Credant Technologies, admitted to Time that online credit services are essentially powerless to this form of mining.
"We have no direct control over the security of these online services, nor is it easy to know who has information about you," Webb told them.
And in October of 2012, 3.6 million Social Security numbers were hacked in South Carolina:
South Carolina newspaper The State wrote about the breach, reporting that 387,000 credit and debit card numbers were exposed. They discovered that while Social Security numbers were encrypted, about 16,000 credit card numbers were not.
So while much of someone's personal data is encrypted and secure, the ways in which security companies protect it are not. And until they are, this kind of thing isn't going away.

