WASHINGTON — When Internet security experts took a close look at Hunters BBS, a Russian-owned hook-up app, they were alarmed.
The security was so rudimentary that anyone with basic computer skills would be able to get access to basic user information within a couple of minutes. Messages, photos, and location information were being transmitted to Russian servers unencrypted.
The timing of the discovery, a few days before the launch of the Winter Olympics in Sochi, made it even more disconcerting. The games earned a reputation as a prime hook-up opportunity during the 2012 games in London, when it became a running joke that an outage of Grindr's network was caused by heavy use, though the company denied that was the cause. But Russia is a different story. Its anti-LGBT legislation, widespread government snooping, and proliferation of vigilante thugs can make it dangerous terrain for online cruising.
BuzzFeed first approached security experts about Hunter BBS after its CEO, Dmitry Tsyvinski, issued a press release on Monday saying that the system had been hacked. The experts detected serious vulnerabilities beyond what Tsyvinski had reported, and asked BuzzFeed to hold this story to give the company time to patch their system, a task that they estimated could take a week of full-time programming. But within 17 hours, Tsyvinski sent a message saying it was fixed, although the app had still not been updated in the iPhone App Store nor in Google Play. The holes in Hunters BBS system remain, and exchanges with Tsyvinski raise doubt as to whether his company knows how to fix them or has the capacity or commitment to doing so.
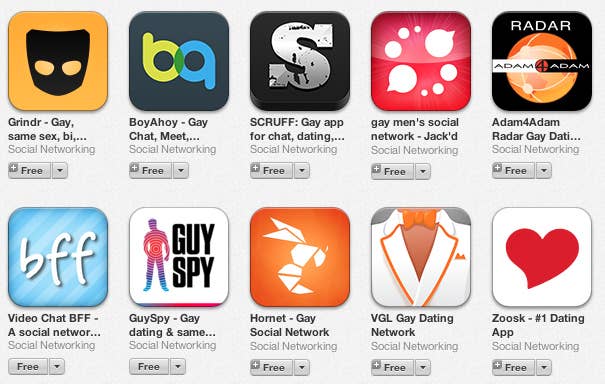
Hunters is a relatively small app in the hook-up app market; it claims a global user base of 1.2 million, but outside experts say it probably has a user base of well under 150,000 based on publicly available information. Even with larger apps, users don't have a good way of knowing who they're trusting with their personal data — G-rated and X-rated pictures, private conversations, GPS coordinates — or what steps companies are taking to protect them from snooping. This is a concern even in countries where LGBT people are relatively safe. In places like Russia, the worries are far more serious.
"I would not use a gay dating app in Russia or the Middle East [or other places with anti-gay laws]…on my phone," said one of the security experts who evaluated Hunters BBS. The expert asked to be kept anonymous because he did not want his company associated with a report that might expose the system's users to be targeted by hackers.
Tsyvinski claimed a cyber attack had deleted the profiles of 72,000 users, blocked access to users around Sochi, and sent thousands of users a message in English that they would be arrested under Russia's law against homosexual propaganda. None of these claims could be independently verified, however, and the University of Toronto's Citizen Lab, which is monitoring internet activity around the Sochi games, found no evidence that the app was blocked. And the law banning "gay propaganda" is technically an administrative offense, punishable by fines, not by arrest. But whether it was a hoax or not, it was clear that users were taking a serious risk by trusting the application with their data.
Even the major players among hook-up apps have shown vulnerability among users in the past. In 2011, a hacker in Sydney, Australia found a vulnerability in Grindr, which now claims more than seven million users worldwide. The hacker compiled a website that listed screennames, passwords, and Grindr contacts for around 100,000 people before Grindr took legal action to shut it down and patched its system.
Today, the app uses "basic security," Grindr CEO Joel Simkhai told BuzzFeed in an interview in November, declining to clarify further. But the app still operates over networks that can easily be monitored.
"Quite frankly, a lot of the [data] goes through WiFi networks and cellular networks — we can't control those," Simkhai said. "The Russian government has a lot of control [of communications] there [and] this is the post-NSA age where we would now realize that everything is very much available, particularly to government."
Hornet, a Seattle-based app that launched in 2011, has highlighted its security protocols in its marketing and has expanded in many countries with laws against homosexuality, including Egypt and Dubai. It is one of the most popular hook-up apps in Russia, claiming 100,000 daily users in Moscow alone.
"We use SSL protocols, which is the same encryption that the banks use," said Sean Howell, the CEO of Hornet. "The NSA has the keys to that, but aside from that it's very difficult to break this."
There are steps users can take for extra precaution. They can use virtual private networks (VPNs), which can reroute data through servers in other countries that may be more secure. One security expert suggested only using apps on a computer through a program that emulates a cell phone — that way, no one can identify users by figuring out their phone numbers.
But even if users take steps to protect data, there is still the chance that someone can hack a device if it is lost or stolen. Even more simply, and more relevant to Russia, users could be entrapped by someone else posing as another user.
Hate groups like Occupy Pedophilia have used social networks to lure gay men into meeting for what they think is a date, only to be kidnapped and humiliated in videos posted online. This has mostly been done through the Russian equivalent to Facebook, VKontakte, but hate groups could easily use hook-up apps the same way.
"I'm afraid they're going to target my users the way they target users on VK," Howell said, referring to VKontakte. The Hornet app sends out messages in Russian warning users to always meet in public, and it even randomly skews location data in the country so that location information can't be used to pinpoint users' locations.
Governments with anti-gay regimes sometimes take steps to block hook-up apps, as recently happened to Grindr in Turkey, but the technology they use to shut these apps down is usually relatively easy to circumvent by using a VPN.
In some countries, governments use apps for low-tech entrapment schemes to arrest gay men.
Scott Long, founding director of Human Rights Watch's LGBT program who is now a visiting fellow at the Harvard Law School, recently documented the story of an Egyptian who was arrested while working in Saudi Arabia. He went to meet someone with whom he'd connected through an online chatroom, and was met by police officers instead. He was given 150 lashes and spent two years in a jail cell with several other prisoners convicted of homosexuality — many of whom were arrested through apps including Hornet, Palringo, U4Bear, and WhosHere.
"All you need is [a] government that takes the issue seriously and wants to track down queers, or you need blackmailers with some level of technological skills … [these apps] will get hacked, it's inevitable," said Long. "The problem is that users really do feel safe."
But that sense of safety is what makes these apps so important in countries where LGBT people are embattled, said Hornet's Howell. These apps are about more than sex in countries where it is the only safe space many gay men can access. They provide a support system for people who would otherwise be isolated, and even prepares them to come out and assert their right to exist.
"We're not an apolitical company," Howell said. "What our apps do in some countries is incredible — it speeds up gay life 30 or 40 years."
Correction: This story incorrectly identified the name of the University of Toronto's Citizen Lab. It is Citizen Lab, not Community Lab.
