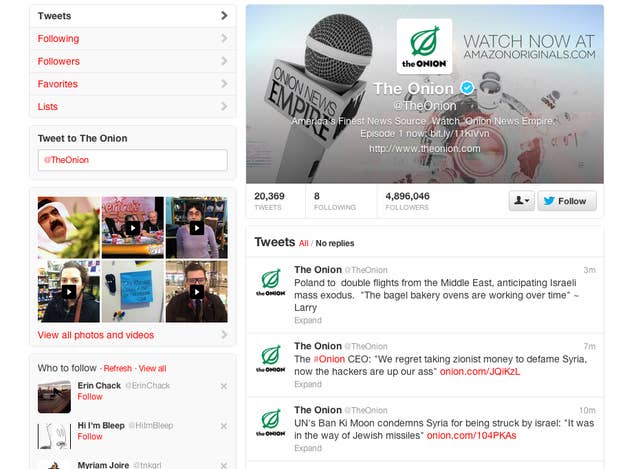
Yesterday, The Onion's tech team penned a blog post explaining Monday's social media hack in elaborate detail. It lays out in plain language exactly out how employees were duped by the Syrian Electronic Army — the hacktivist group that's been terrorizing major media outlets for weeks now. BuzzFeed was targeted with an identical attack last week.
The takeaway: This was hardly a hack. This was a series of tricks — of small lies, fake links, and webpages, and simple human deception.
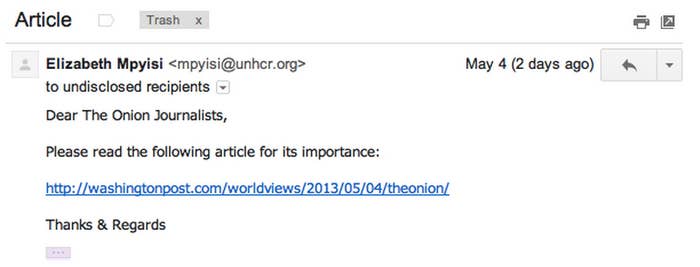
The hack, technically, was a three-part phishing scam. It started with fake emails from the Washington Post, which contained links to a fake Google Apps log-in screen. The hackers used this to gather passwords, gaining access to at least one email account. The hackers then used that email to send out interoffice emails using the same URL. This second attempt — which came from a trusted, familiar source — fooled at least two more employees.
With multiple compromised accounts, the hackers sent one last phishing email from an in-office account, disguised as an IT email urging employees to change passwords. This was the attempt that tricked an employee with access to The Onion's Twitter account into revealing him/herself.
This is what a modern hack looks like. It's not elaborate or flashy at all, and requires minimal technical skill. There are no mainframes, or expensive servers, or giant green screens of code. If you have the know-how to make a fake Gmail account page and one or two disguised, redirecting URLs, you have the chops to hack The Onion too — or the AP, or 60 Minutes, or CBS, or The Guardian, all of whom fell victim to the SEA in recent weeks.
Much more important is human research. "These attackers do their homework," RSA security expert Daniel Cohen told BuzzFeed earlier this week. "Once they pick their organization, they pinpoint an individual and send emails that are directly related to something in their lives. They use information that is readily available through Facebook or LinkedIn and use that information against you."
While extra measures like two-factor authentication can help to protect again attacks like this, the only foolproof way to stay secure is to understand how these types of phishing scams work. Rather than expensive and elaborate security systems, the best line of defense for major media organizations is to entrust the most sensitive passwords only to employees who know how this kind of attack works.
People with, for lack of a better term, internet street smarts.
